Iran’s cyber escalation: Critical U.S. infrastructure in the crosshairs

Iran’s cyber escalation: Critical U.S. infrastructure in the crosshairs📷 Published: Apr 7, 2026 at 23:04 UTC
- ★FBI, NSA, CISA issue rare joint warning on Iranian hackers
- ★Energy, water, and transport sectors face heightened risk
- ★Geopolitical tension now a direct cybersecurity cost for operators
The warning isn’t theoretical. Iranian cyber groups, according to the advisory, have shifted from reconnaissance to ‘hands-on-keyboard’ activity—directly manipulating programmable logic controllers (PLCs) in critical infrastructure. These aren’t just data breaches; they’re attempts to disrupt physical operations, from power distribution to water treatment. The escalation ties directly to the U.S.-Israel conflict, with Tehran’s proxies treating cyber as a low-risk, high-impact retaliation tool.
For operators, this means an immediate shift in threat modeling. The CISA alert highlights vulnerabilities in Schneider Electric and Omron PLCs—hardware ubiquitous in industrial settings. Patching these systems isn’t like updating a laptop; it requires downtime, vendor coordination, and often manual intervention. The cost isn’t just financial; it’s operational paralysis during the fix.
The market context here is brutal. Critical infrastructure providers already face aging tech stacks, underfunded security teams, and a talent drain to higher-paying sectors. Now they’re staring down nation-state actors with no profit motive—just disruption. Insurance premiums for cyber coverage in these sectors spiked 28% in 2023, and this advisory will only accelerate that trend.
The real-world price of a war fought in code and control systems📷 Published: Apr 7, 2026 at 23:04 UTC
The real-world price of a war fought in code and control systems
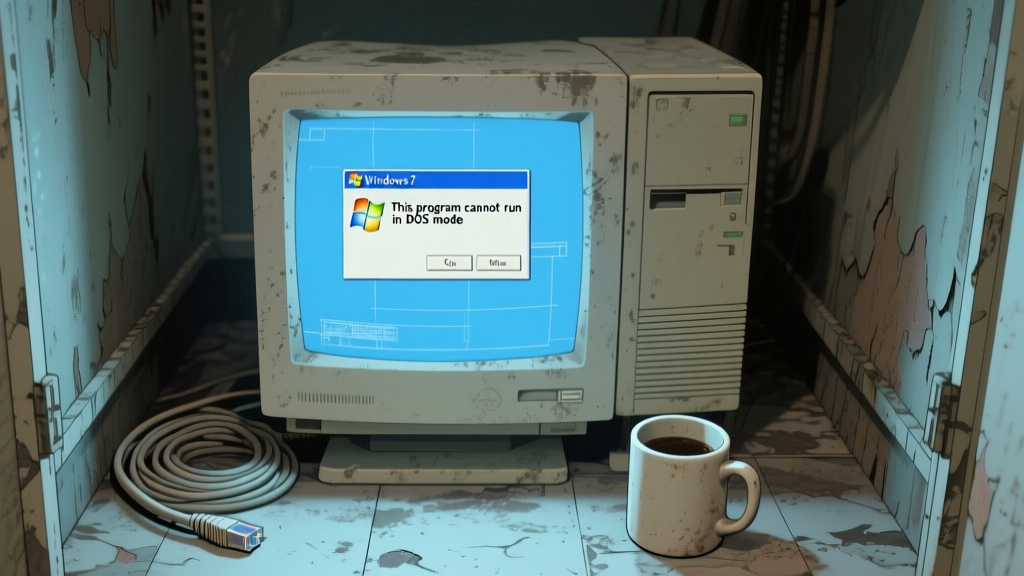
The user reality cuts deeper than specs. A water treatment plant operator in Texas told TechAnd that their team still relies on Windows 7 machines to monitor PLCs—‘because the vendor never certified anything newer.’ That’s the gap exploits like this thrive in. The advisory urges network segmentation and multi-factor authentication, but for plants running 24/7, even basic hygiene is a scheduling nightmare.
Ecosystem effects ripple outward. Suppliers like Schneider Electric now face pressure to accelerate firmware updates—but their customers can’t absorb rapid changes without breaking compatibility. Meanwhile, cybersecurity firms pitching OT-specific solutions (think Dragos or Nozomi Networks) will see demand surge, but deployment cycles in industrial settings measure in months, not days.
The second-order impact is behavioral. Boardrooms that treated OT security as an IT afterthought are now confronting direct liability. A successful attack on a dam or grid wouldn’t just cause outages—it would trigger regulatory crackdowns, shareholder lawsuits, and reputational fallout that lasts years. The Colonial Pipeline ransomware attack in 2021 cost $4.4 million in ransom; the indirect costs topped $50 million in lost productivity and emergency measures.