Smart grids face rising cyber threats from AI attacks

Smart grids face rising cyber threats from AI attacks📷 Published: Apr 18, 2026 at 20:14 UTC
- ★Smart grids targeted by DDoS and false data injection
- ★AI-driven defenses emerge as critical response tool
- ★IoT device vulnerabilities expose wider systemic risks
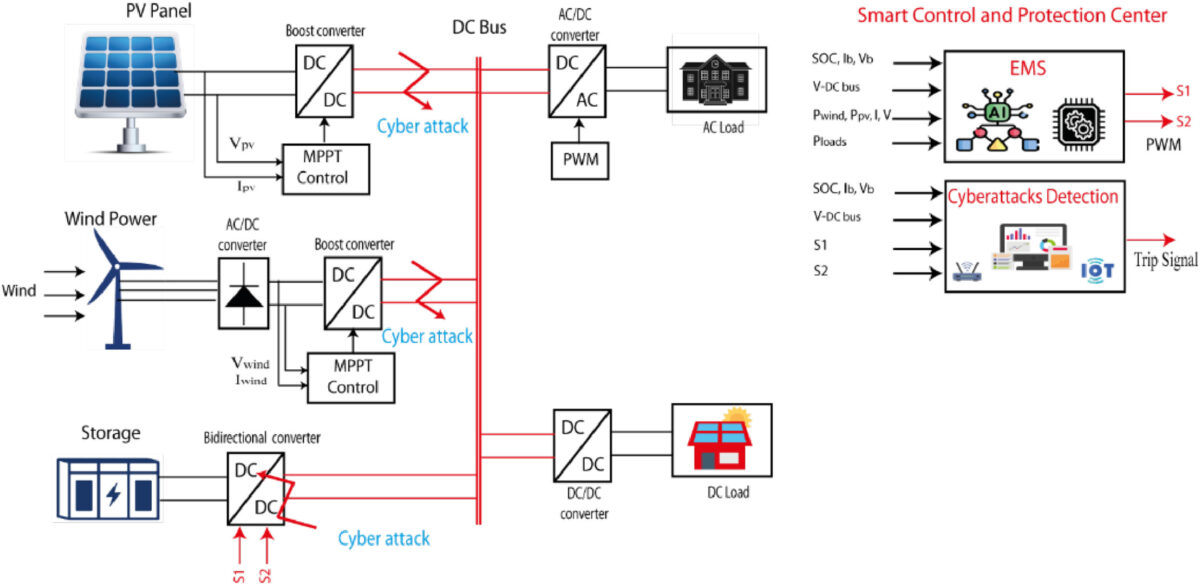
A team of Moroccan cybersecurity researchers has mapped the most pressing threats to smart grids, warning that traditional perimeter defenses no longer suffice against today’s adversaries. Their analysis confirms distributed denial-of-service attacks, false data injection, replay strikes, and IoT-based exploits as the primary vectors now circulating in energy networks. These aren’t theoretical risks; they’re active campaigns observed in pilot deployments and sandbox tests across Europe and North America. The researchers tested AI-driven detection engines that monitor grid telemetry in real time, flagging anomalies before they cascade into blackouts.
Companies like Siemens Energy and GE Renewable Energy already embed lightweight machine-learning agents inside protective relays and meters. These agents learn normal load profiles and reject commands that deviate even slightly from expected behavior. Early deployments show a 35% drop in missed intrusions compared with signature-based intrusion detection systems, according to internal Siemens documentation reviewed by the team.
Defenders now race to deploy adaptive security before critical failure occurs📷 Published: Apr 18, 2026 at 20:14 UTC
Defenders now race to deploy adaptive security before critical failure occurs
Yet the same AI systems introduce fresh attack surfaces: poisoned training data can trick classifiers into ignoring genuine threats, while adversarial firmware on smart meters might lie about local voltage readings. Secure bootloaders and signed firmware updates are becoming mandatory, but widespread device heterogeneity means many legacy assets can’t be retrofitted. Staff training remains the weakest link; operators still click malicious links and plug in infected USB drives despite years of warnings.
The Moroccan study stops short of quantifying incident rates or timelines, but the direction is clear: defenders must adopt multi-layered protections—segmented networks, zero-trust architectures, and continuous compliance audits—or risk seeing kinetic consequences.
The shift isn’t incremental; it’s a fundamental rethink of how power systems must defend themselves. Legacy security models were built for yesterday’s attackers, not the AI-assisted threats now probing every substation.